Container escape is an exploitative technique in which an unauthorized individual gains entry to the underlying host operating system from inside a container. This illicit access enables them to breach the container’s isolated environment and potentially manipulate or access resources on the host system. If container escape is successfully executed, it can jeopardize the security of other containers residing on the same host and potentially compromise the entire infrastructure.
Despite these challenges, containerization remains a popular and valuable technology. Many of these issues can be addressed with careful planning, proper tooling, and ongoing management practices. To address these security challenges, organizations use various tools and practices, including container security scanners, CSPM solutions, runtime protection tools, network security policies, access controls, and security best practices tailored to containers.
How does CSPM address these unique security challenges?
CSPM addresses the unique security challenges introduced by containers through its holistic approach. It provides complete visibility into containerized environments, constantly monitors for misconfigurations, compliance violations, and vulnerabilities, and automatically enforces security policies. This proactive stance ensures that dynamic, short-lived containers are always configured securely. Additionally, CSPM integrates seamlessly with DevOps, promoting security throughout the development and deployment process, thus mitigating issues early. It offers real-time alerts and automates incident response, enabling quick reactions to security threats within containers. This combination of continuous monitoring, proactive configuration management, and integration into the development life cycle allows CSPM to effectively tackle the challenges of container security.
Now that we understand the unique security challenges of a containerized environment and how CSPM addresses these concerns, let us explore the onboarding aspects of containers to a CSPM tool.
Onboarding containers to CSPM tools
Onboarding containers to a CSPM tool refers to the process of integrating containers into the CSPM tool for enhanced security monitoring and management. The onboarding process involves configuring the CSPM tool to scan, assess, and protect containers against security risks and compliance violations.
Note
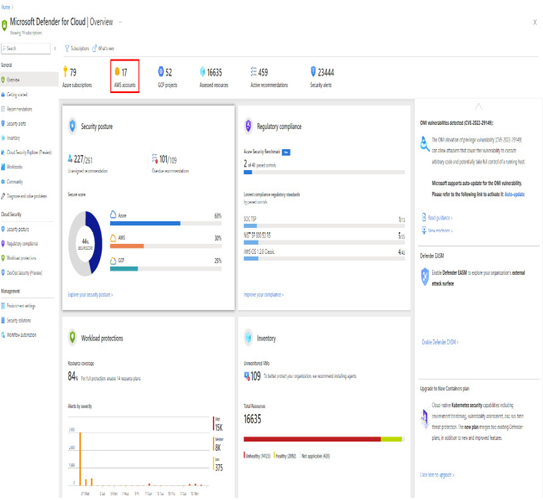
To make the concept easily understandable, the Microsoft Defender for Containers feature of the Microsoft Defender for Cloud tool is taken as a reference wherever it is imperative to explain with an example. There are many other tools available on the market that offer container security posture management features as well. The example chosen here is purely based on publicly accessible information.